Creating and Rotating Encryption Keys
Deeper DiveFor more in-depth information, check out our detailed documentation on the following topics:
Encryption & Key ManagementEncryption KeysKey Rotation
Need any help?If something in this tutorial isn't working as expected, feel free to contact our support team via Slack.
Below is a text-only guide for users based on the above video
What is an Encryption Key?
Akeyless is an all-in-one platform for Secrets Management with the ability to generate, rotate, and delete encryption keys as necessary. To do this, we use a proprietary technology called DFC - Distributed Fragments Cryptography. The technology works by creating a key as fragments on various cloud platforms. These fragments are never combined, not when encrypting nor when decrypting Secrets.
Encryption keys are used to encrypt or decrypt any type of data. That could be personal data or any other type of password or Secret. This can be for data that is either at rest or in transit. Generally speaking, there are two types of cryptographic algorithms - symmetric and asymmetric. An example of a symmetric keys is an AES Key and an example of an asymmetric key is an RSA keys, where you have a public and a private key. An AES key is symmetric in which the same key is used to encrypt as well as decrypt that data.
In this example, we will use an AES Key to demonstrate.
Create an AES Key via the UI
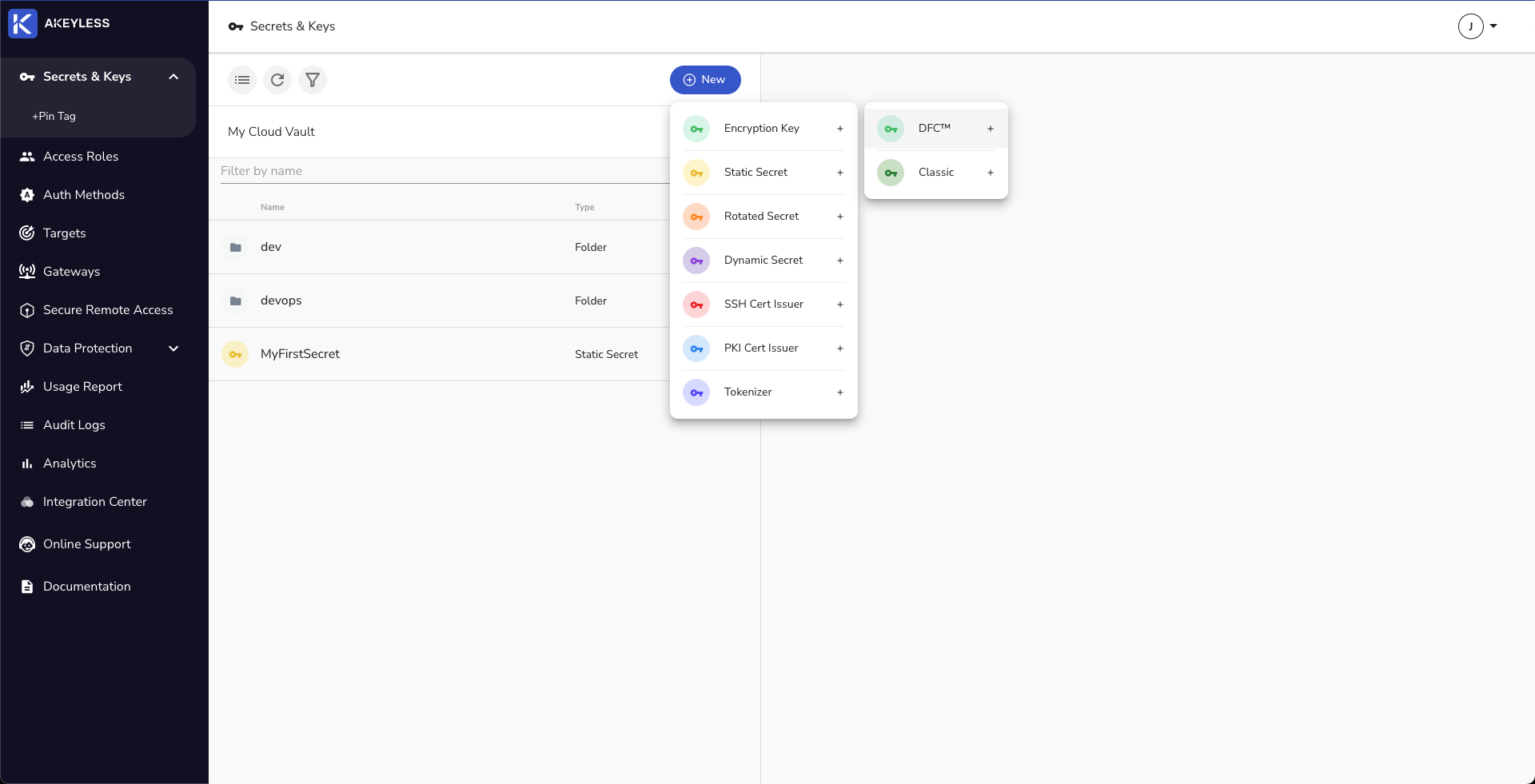
Choose ‘New’ → ‘Encryption Key’ → ‘DFC’
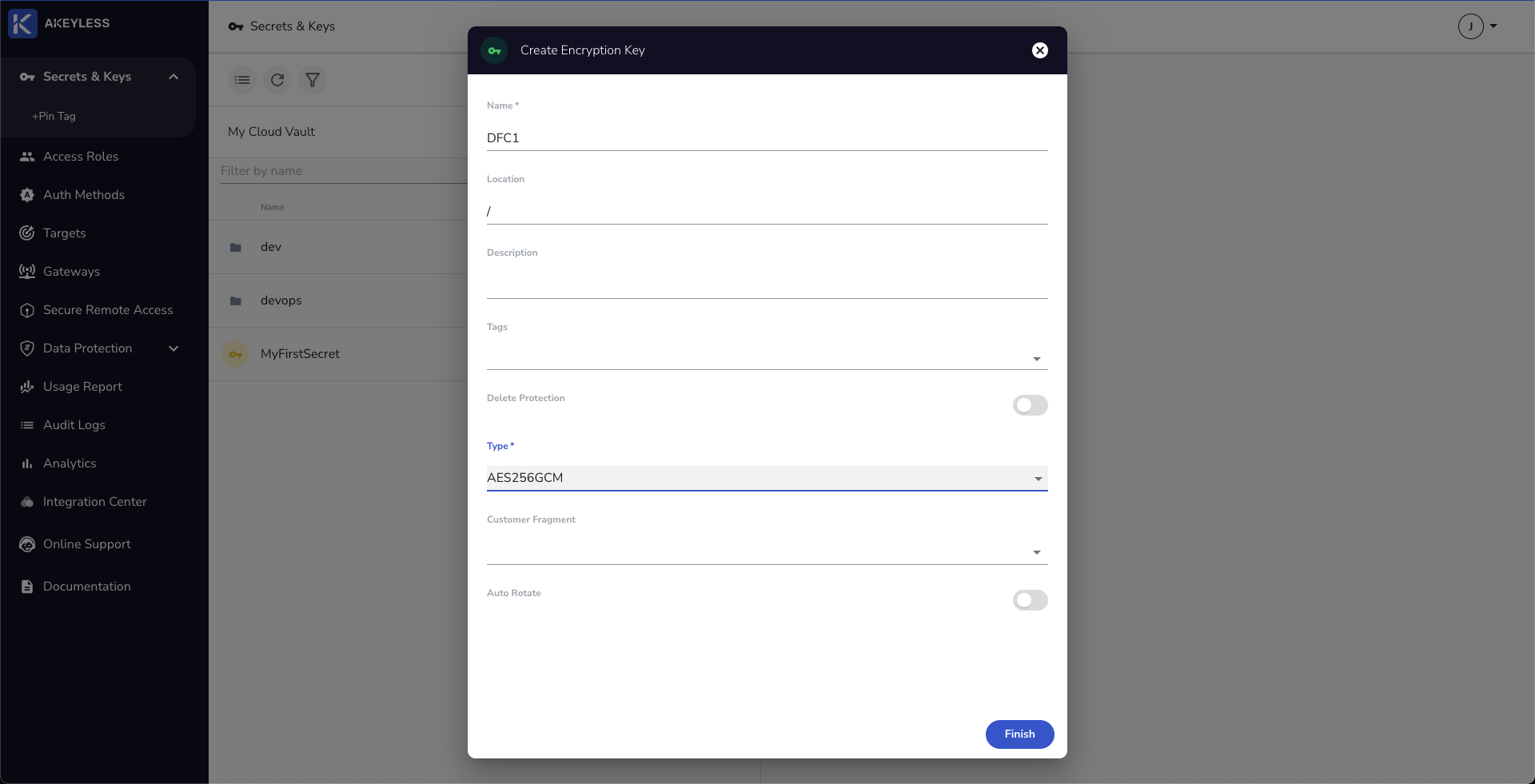
Choose the name and Type of encryption key. There is an option to auto-rotate a key as well (between 1-365 days).
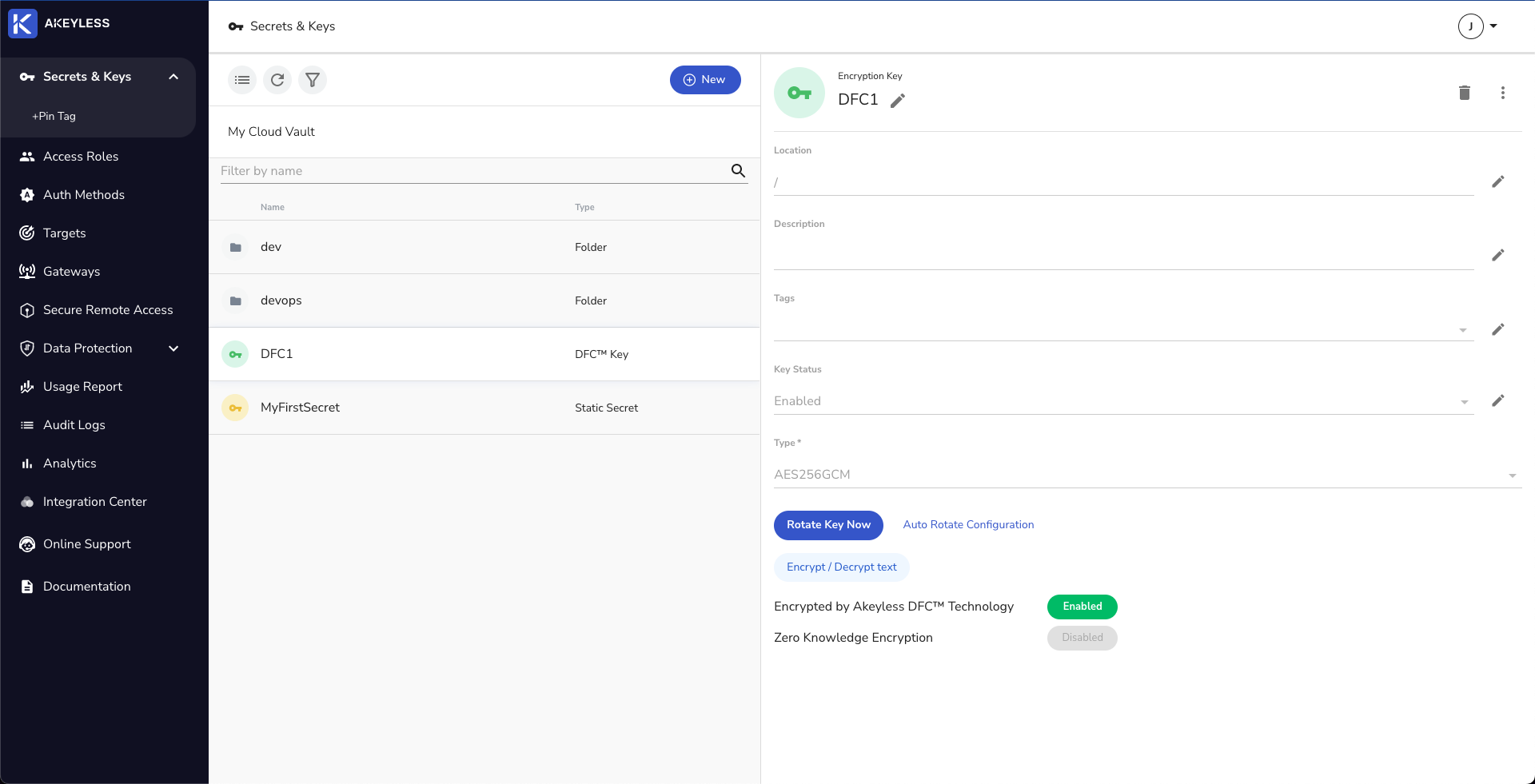
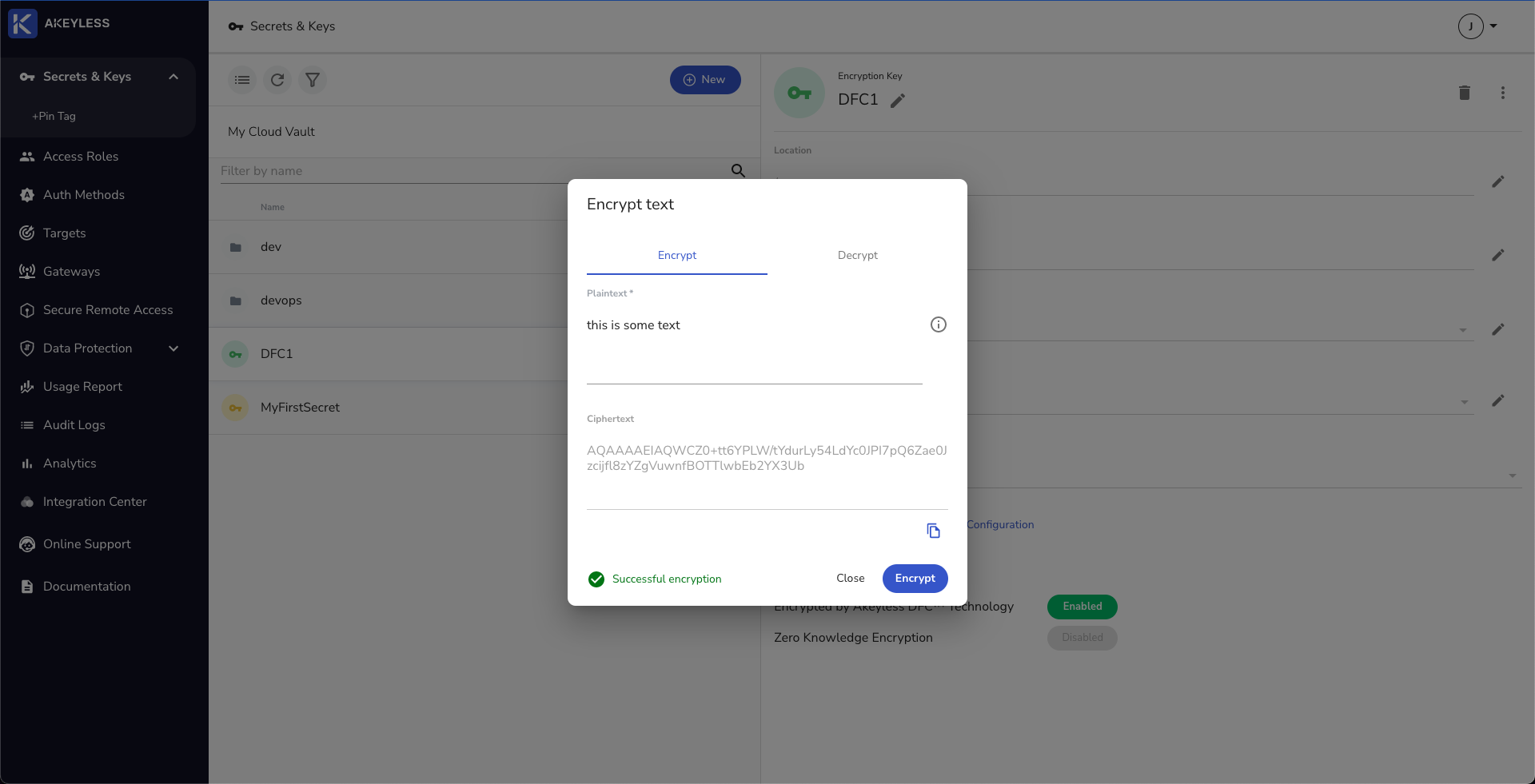
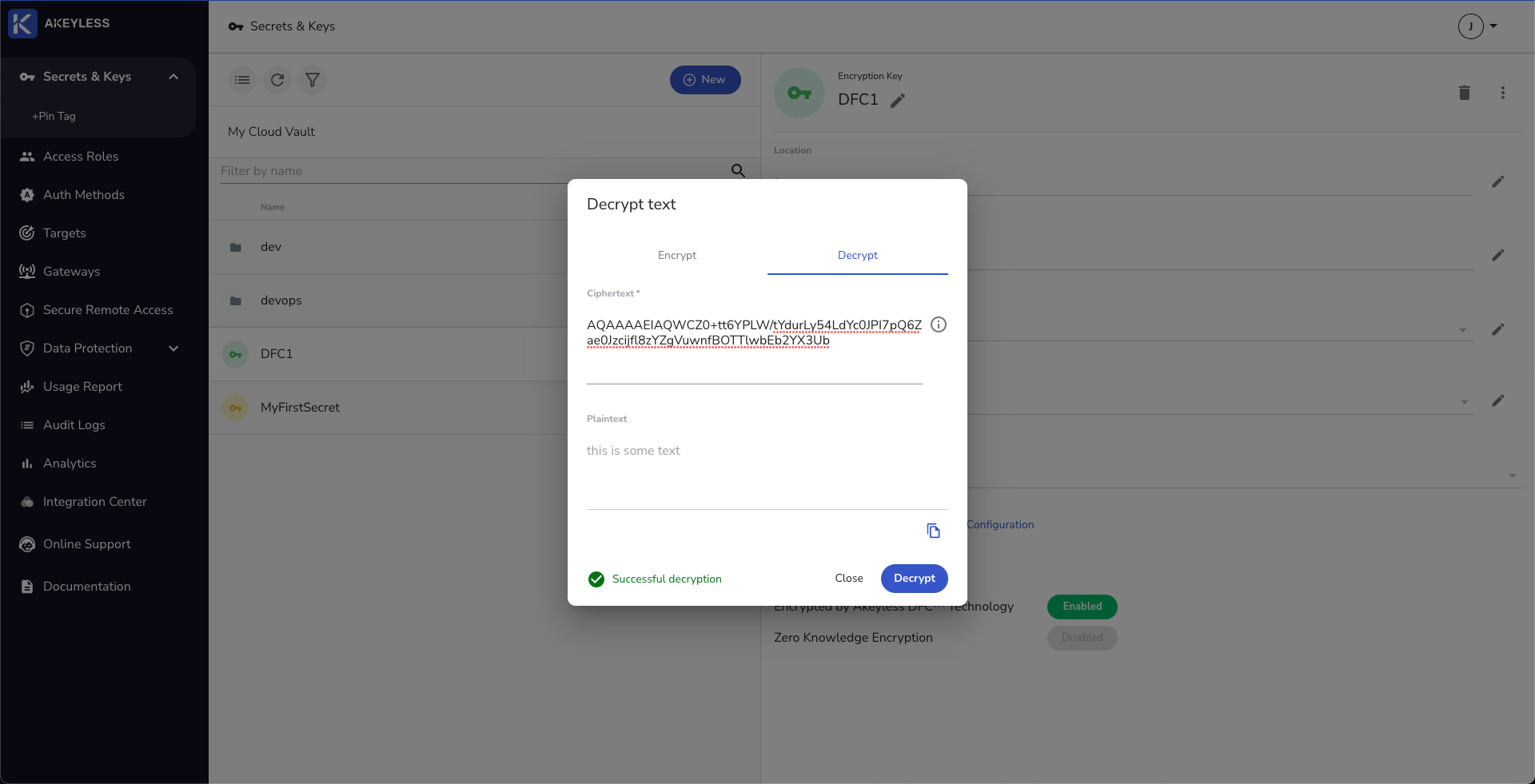
To test the encryption key, you can click the ‘Encrypt / Decrypt Text’ button and choose some text.
Create an AES Key via the CLI
Run the below command for an AES256 key.
akeyless create-dfc-key -n [key_name] -a AES256GCM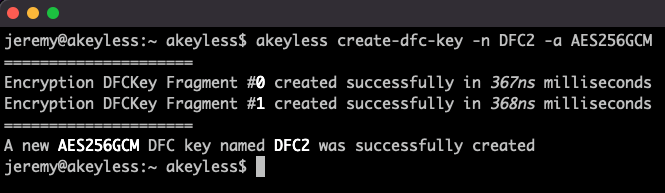
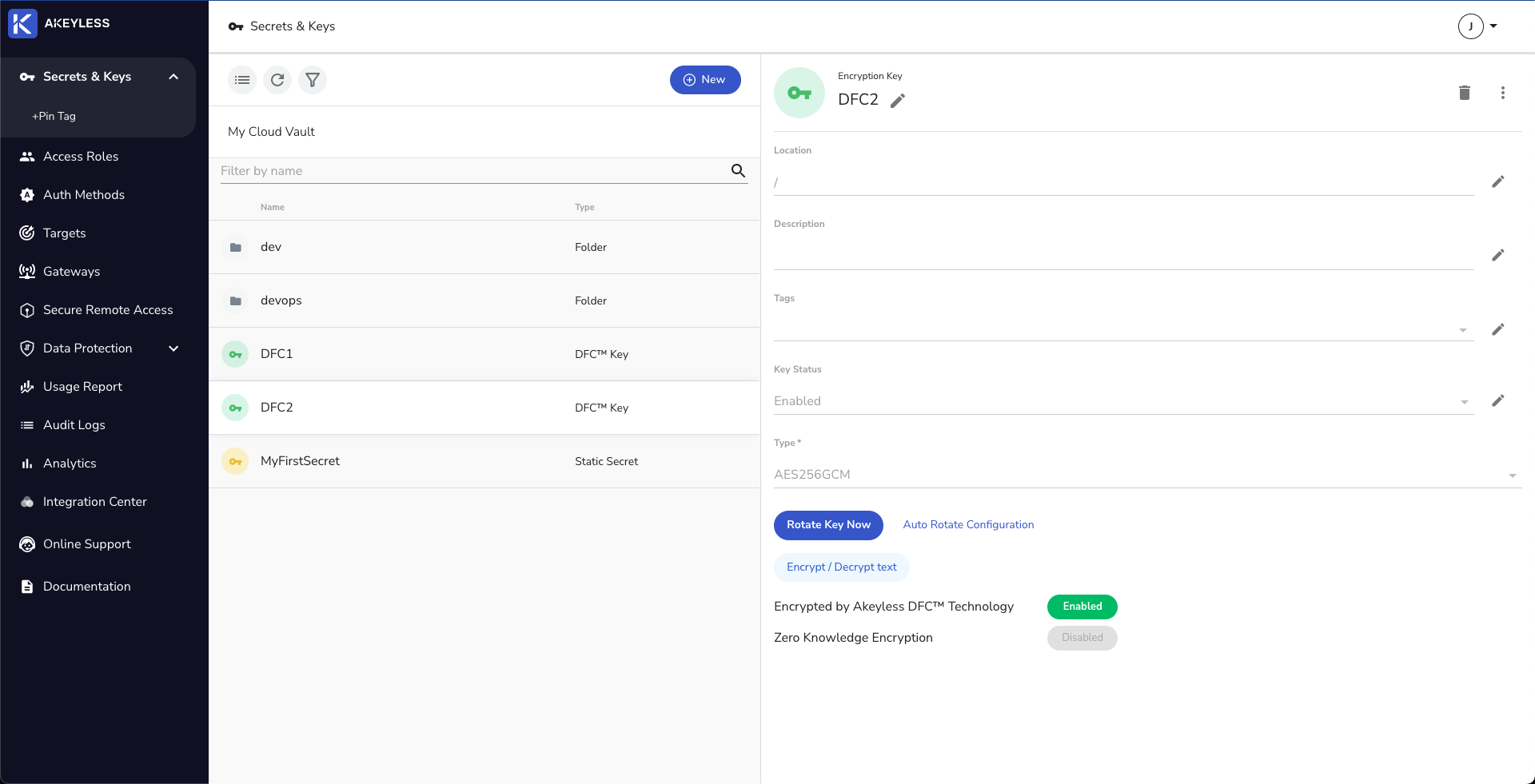
And you can see the key created in the UI as well:
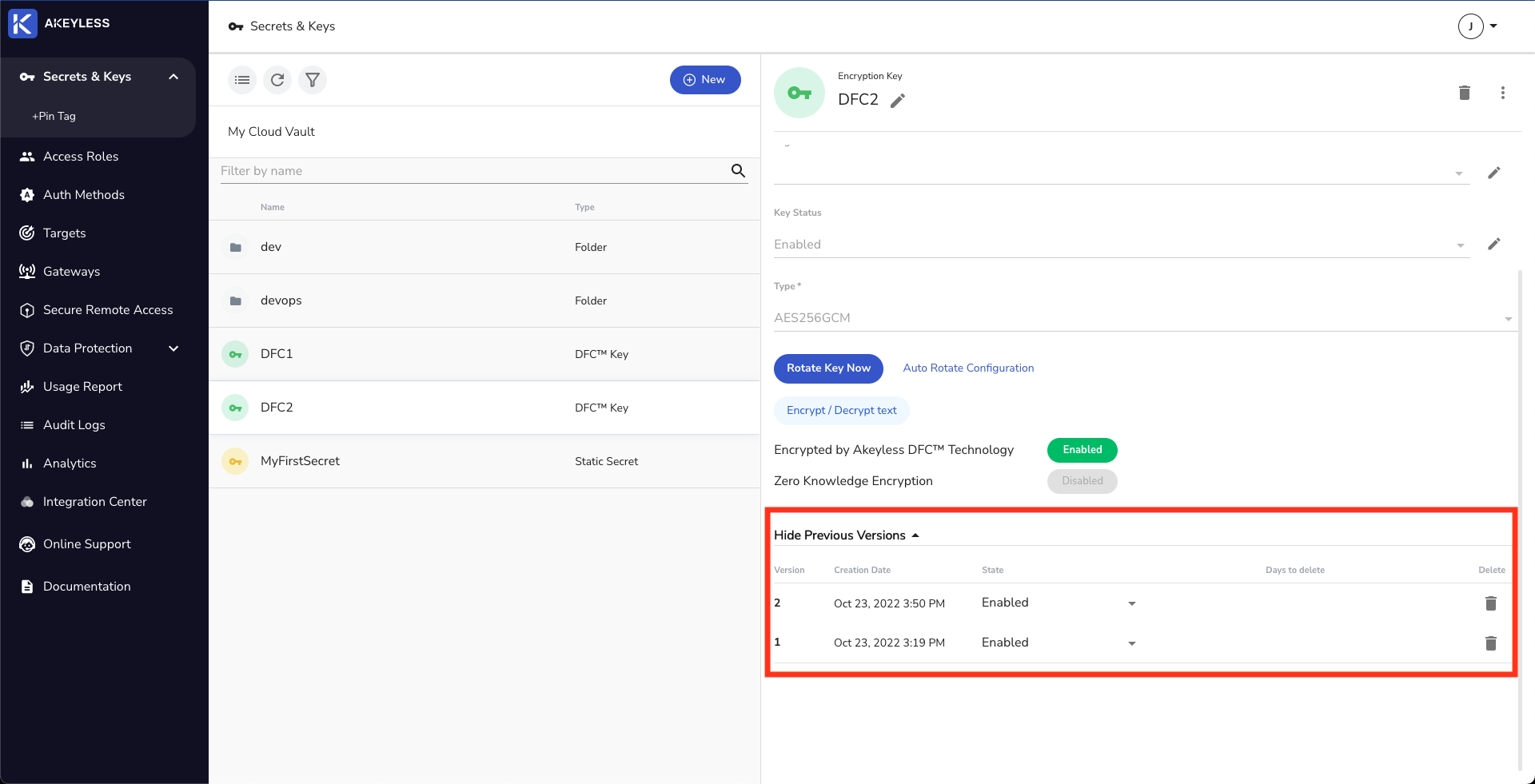
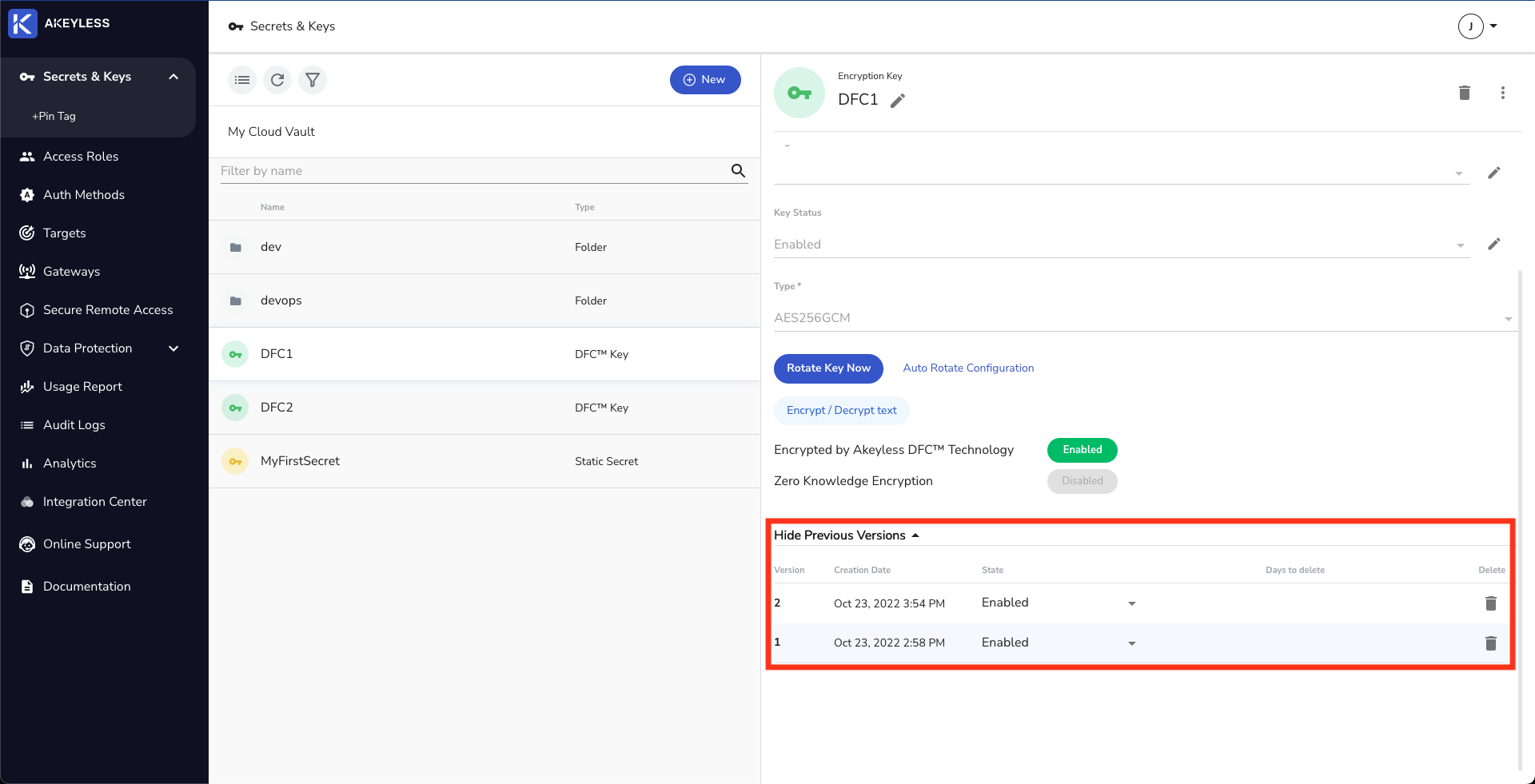
Rotate an AES Key using Akeyless Console
Click the ‘Rotate Key Now’ button. You will also be able to see previous versions of the key below.
Rotate an AES Key using Akeyless CLI
Run the following command:
akeyless rotate-key -n [key_name]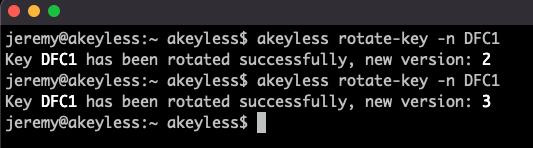
This can also be seen in Akeyless Web Console.
Running the below command will show details of the key, including its name, type, and latest version.
akeyless describe-item -n [key_name]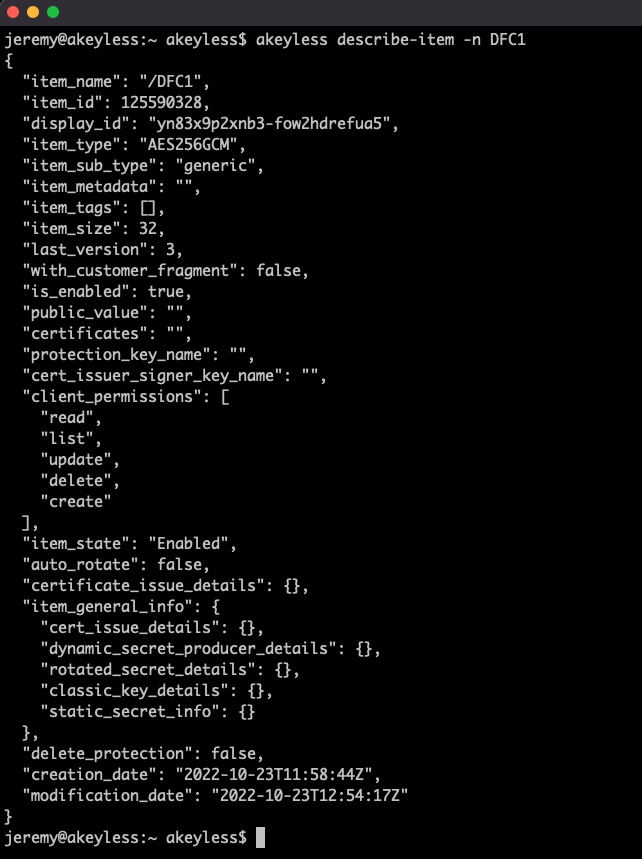
Updated over 1 year ago
