Creating and Using Dynamic Secrets
Deeper DiveFor more in-depth information, check out our detailed documentation on the following topics:
Dynamic SecretsDatabase Dynamic SecretAWS Dynamic Secret
Need any help?If something in this tutorial isn't working as expected, feel free to contact our support team via Slack.
Below is a text-only guide for users based on the above video
What is a Dynamic Secret?
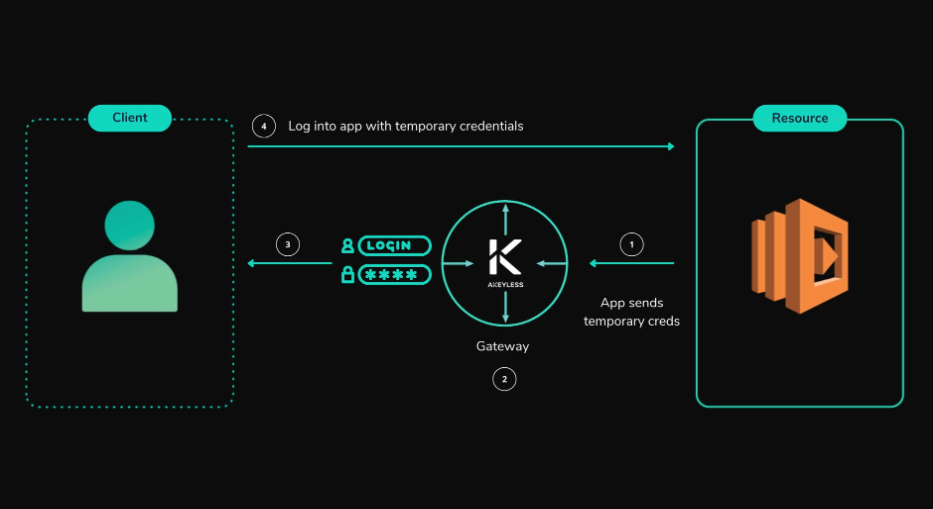
Dynamic Secrets eliminate the need for any long-lived, standing credentials like static secrets. They work by requesting a new temporary user and password from the application or resource being accessed, delivering them just in time to be used for a specific duration, and then deleting them once expired, never to be used again.
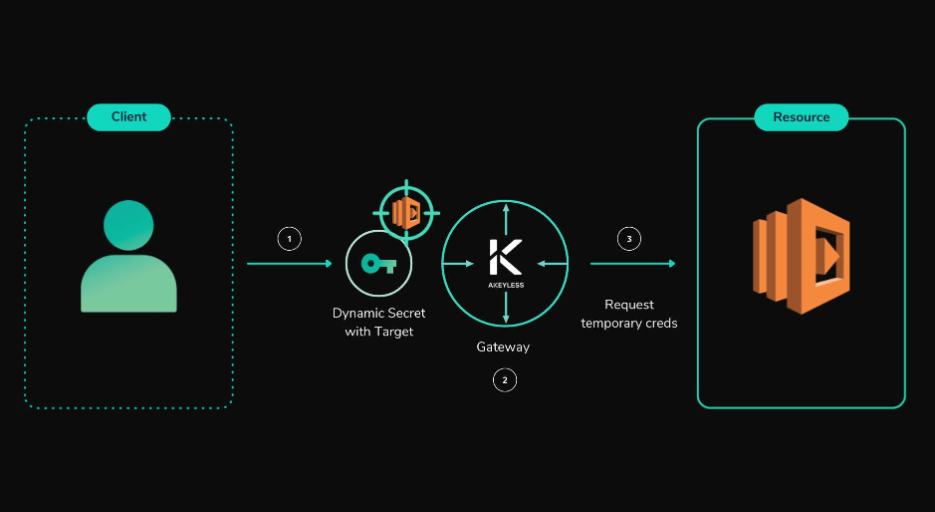
The customer requires Dynamic Secrets for temporary credentials to access resources. By using the Target along with the Gateway, Akeyless requests a temporary username and password from the resource, which it retrieves and then sends back to the user.
Before we get into creating and using Dynamic Secrets, there are a couple of prerequisites to keep in mind. Our gateway needs to be running on an HTTPS endpoint, as using an HTTP endpoint can cause issues when creating Dynamic Secrets from the console. Your target must also be configured with the correct privileged credentials for this to work properly.
Now let’s create our secret.
Creating a MySQL Dynamic Secret via the UI
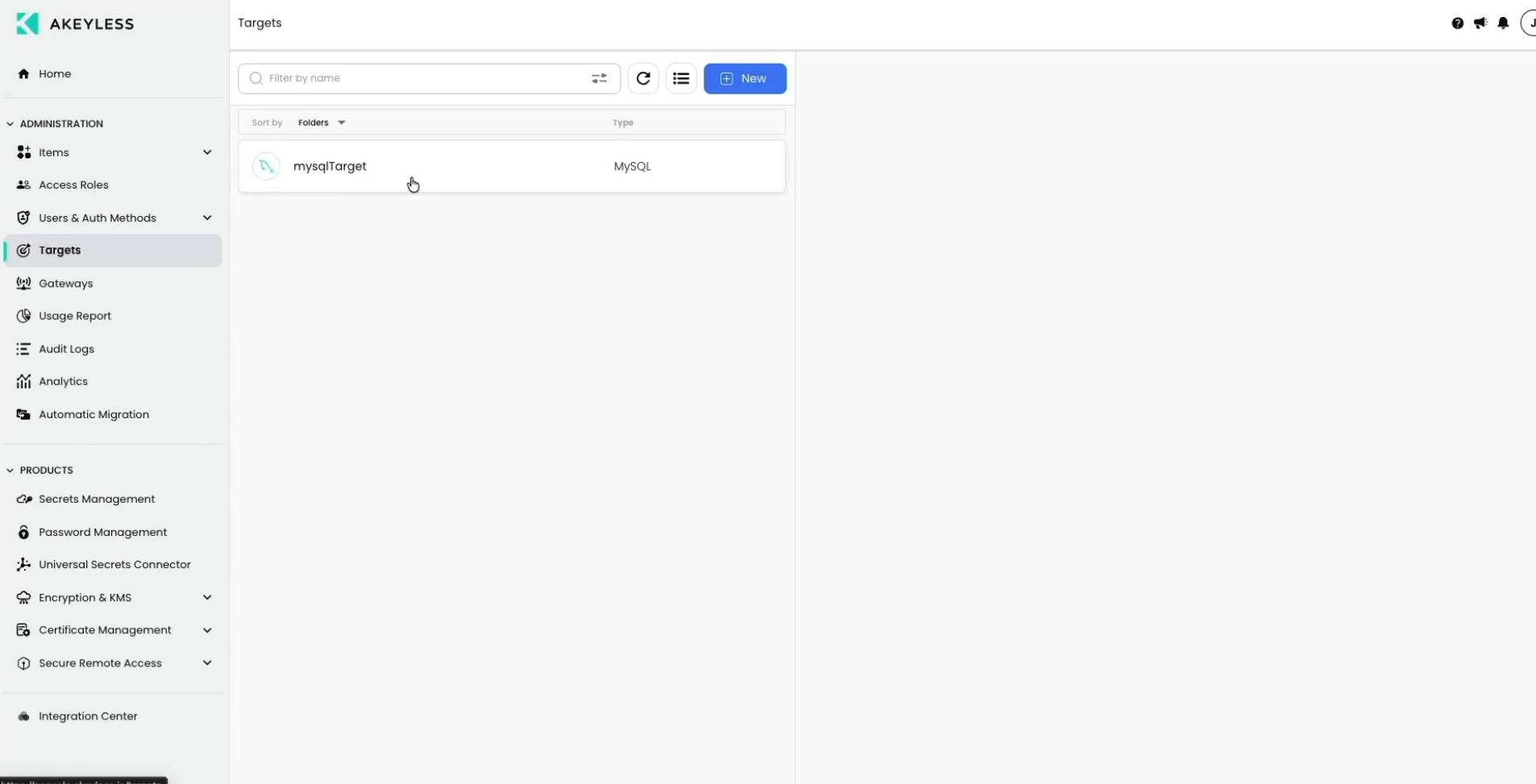
First, here is our Target.
Now, go to ‘Items‘ and click ‘New’ --> ‘Dynamic Secret’.
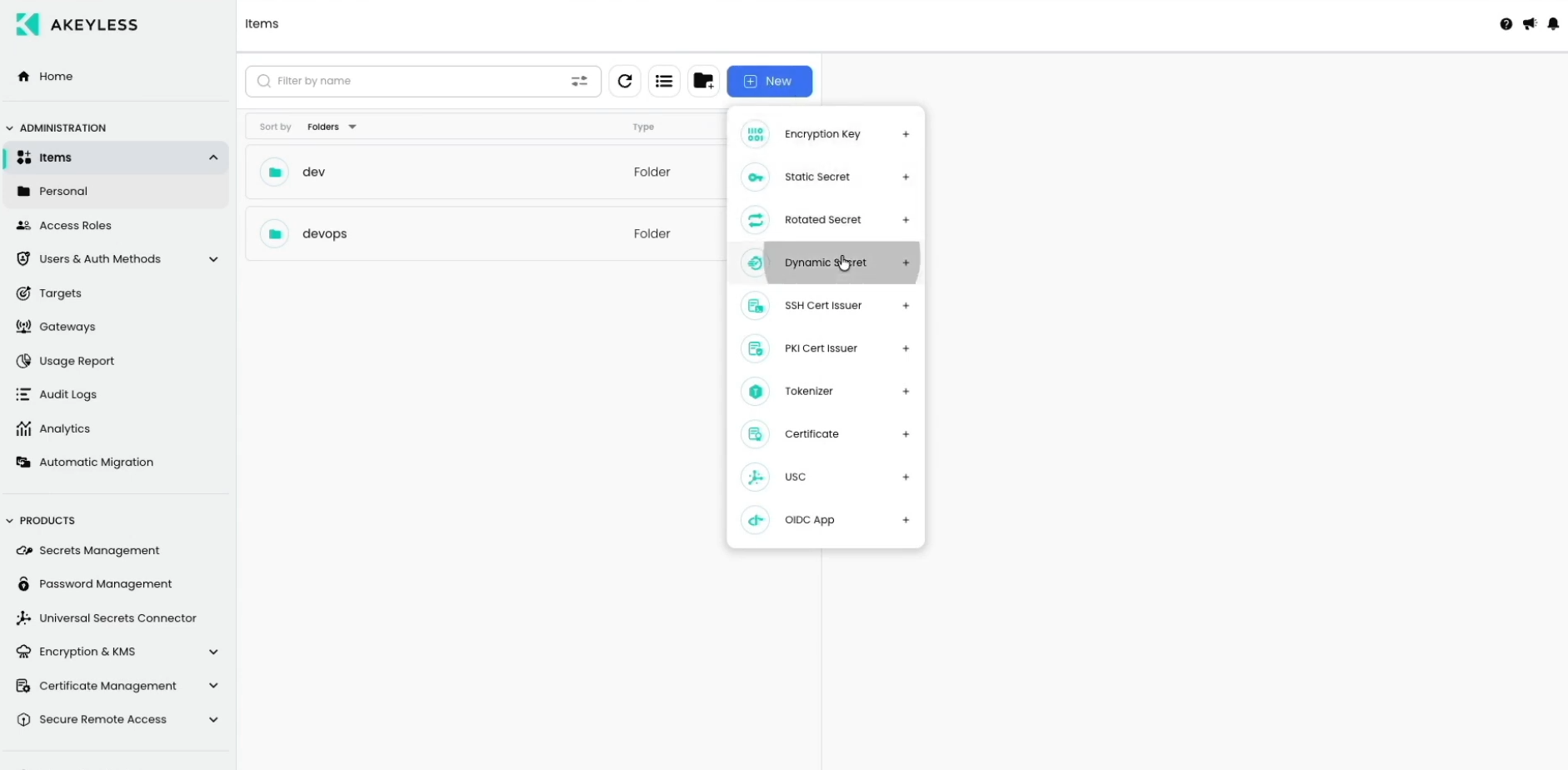
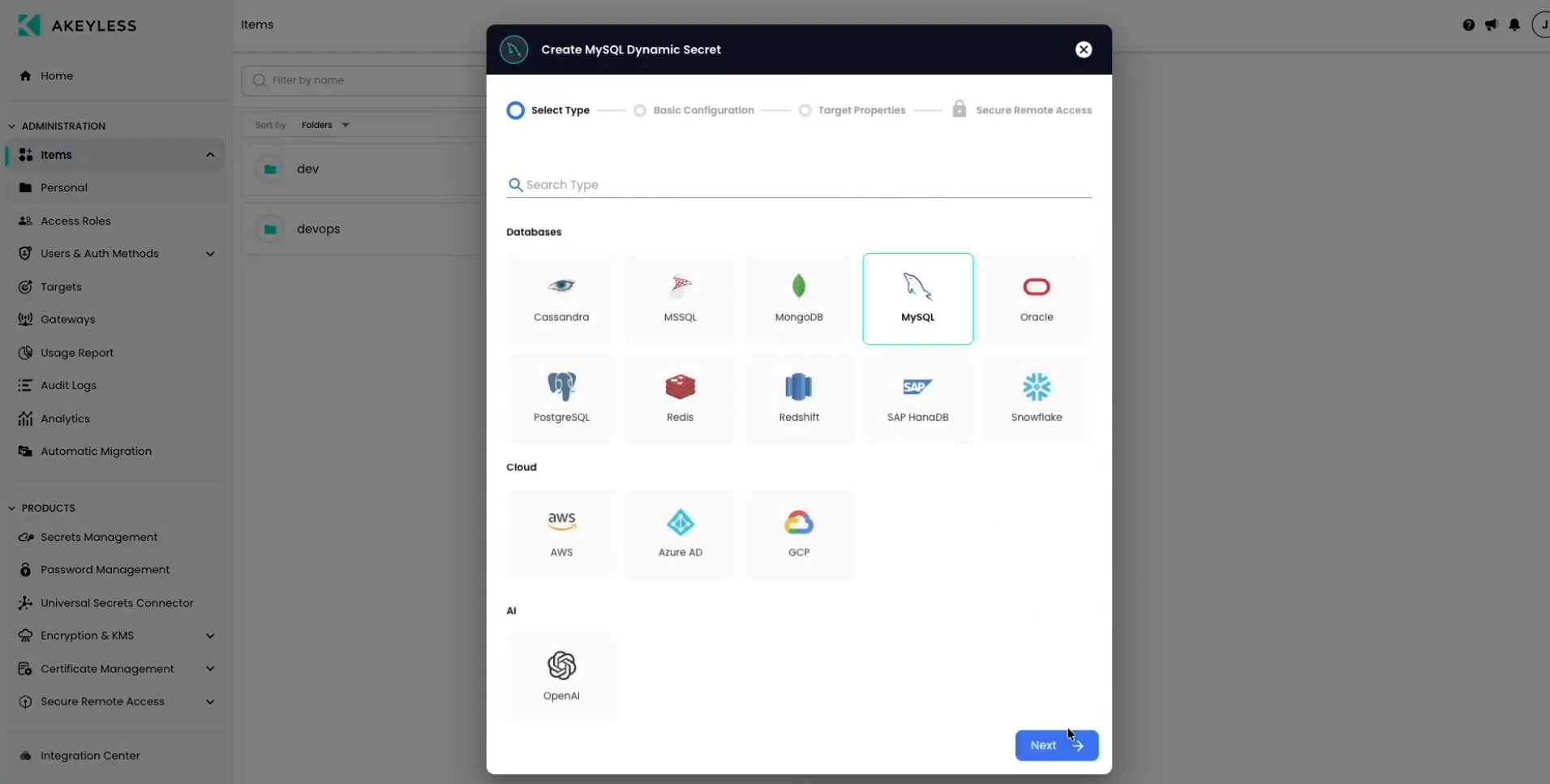
Choose 'MySQL' from the list, then click ‘Next’.
On the next screen, add the required details as follows:
- Dynamic Secret Name
- In "Choose an existing target", choose the MySQL Target we created in the last video
- For the Creation Statement , ensure it matches a new user creation for your version of MySQL
- Time To Live (TTL) for the Dynamic Secret
- Choose your Gateway
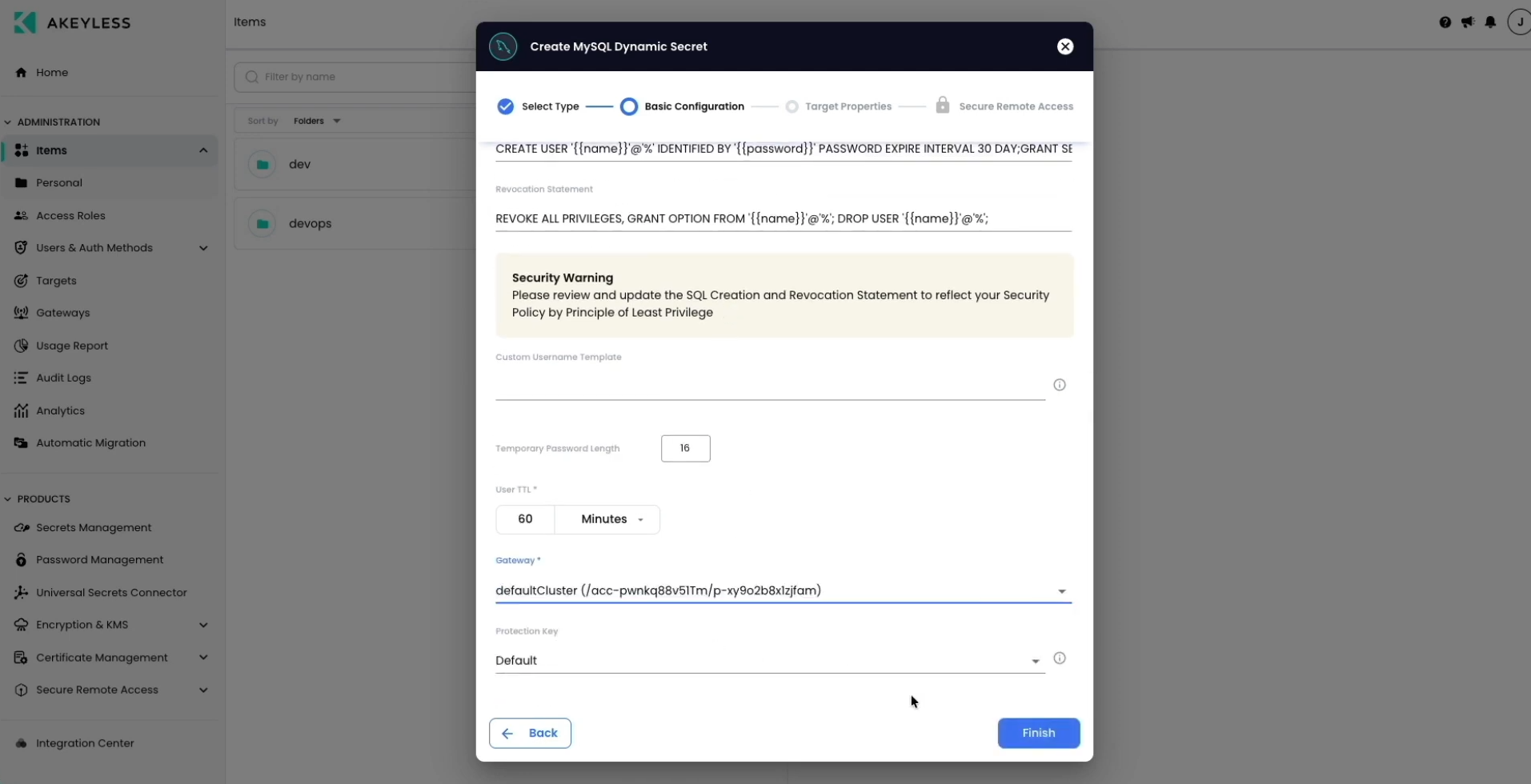
Then click 'Finish'.
You can now see the Secret in your Console under 'Items'.
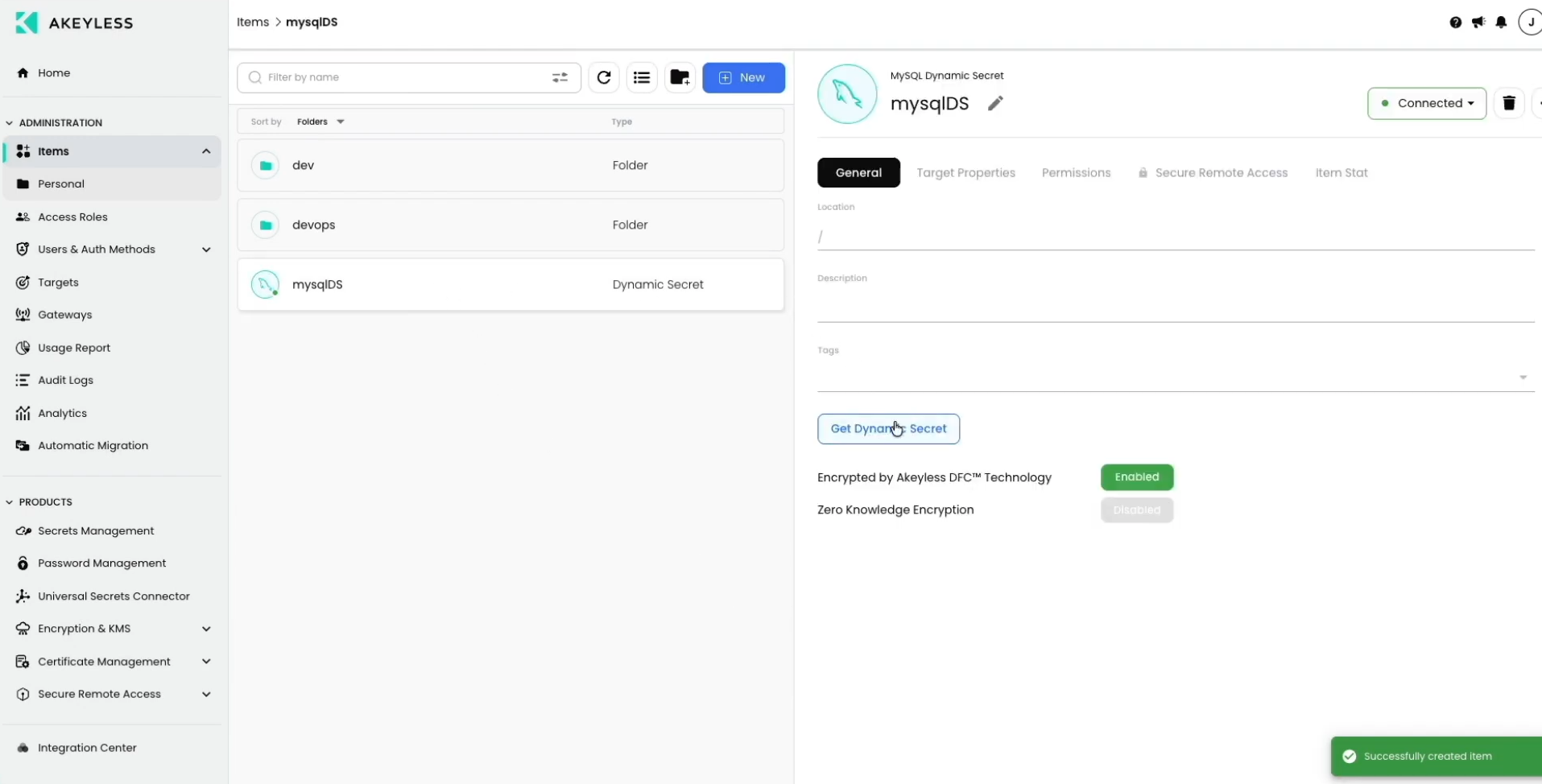
Get a New Dynamic Secret via the UI
Click the ‘Get Dynamic Secret’ button which will then pop up a message showing your information to use for logging into that MySQL instance with access to the specific database.
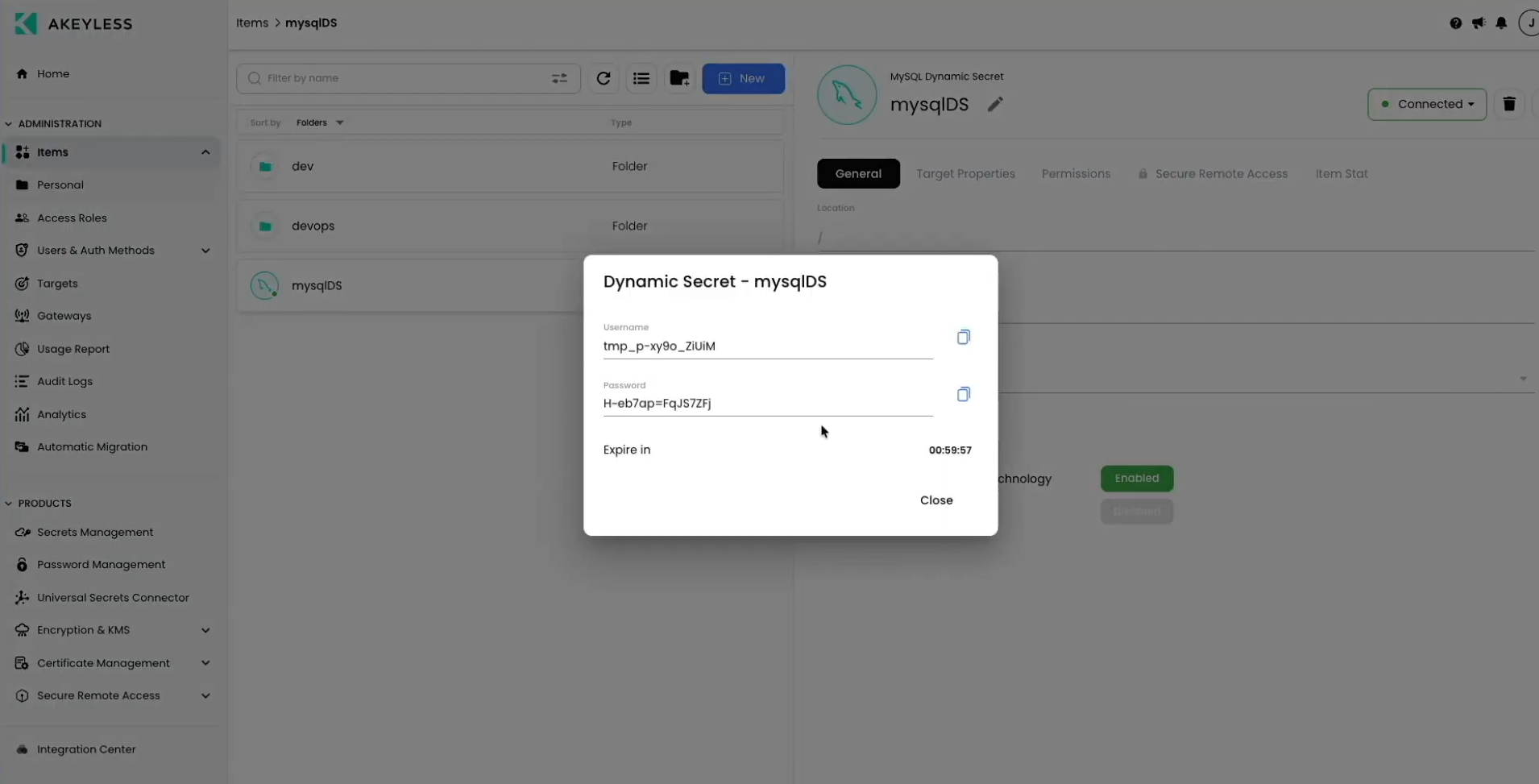
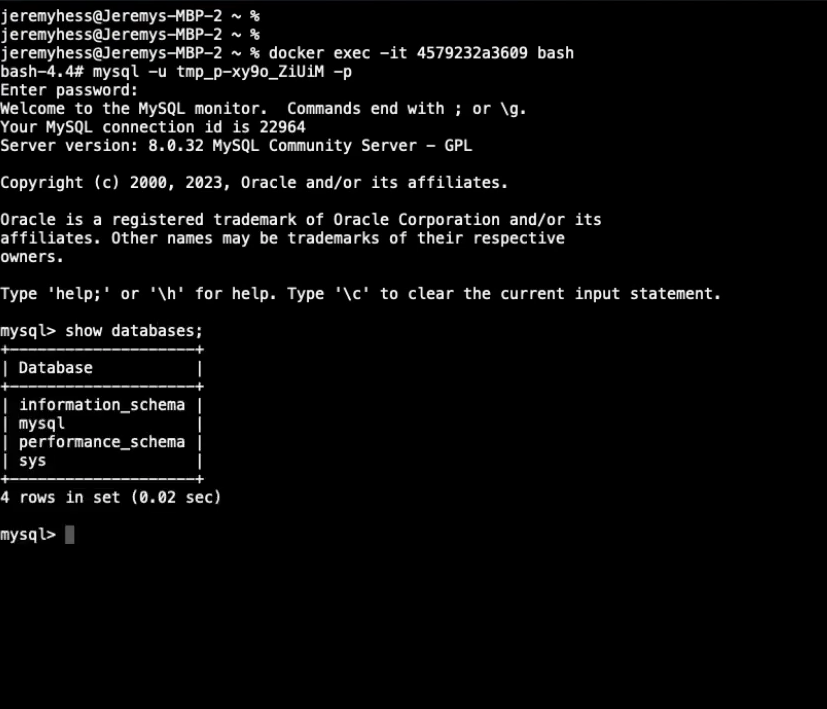
You can now use those credentials to login.
Creating an AWS Dynamic Secret via the CLI
Go to your terminal and run the following command:
akeyless dynamic-secret create aws --name <name_of_dynamic_secret> --target-name <your_target_name> --gateway-url <gateway_URL> --aws-access-mode <iam_user | assume_role (depending on your preferred option)> aws-user-console-access <true | false>You will then see the following:
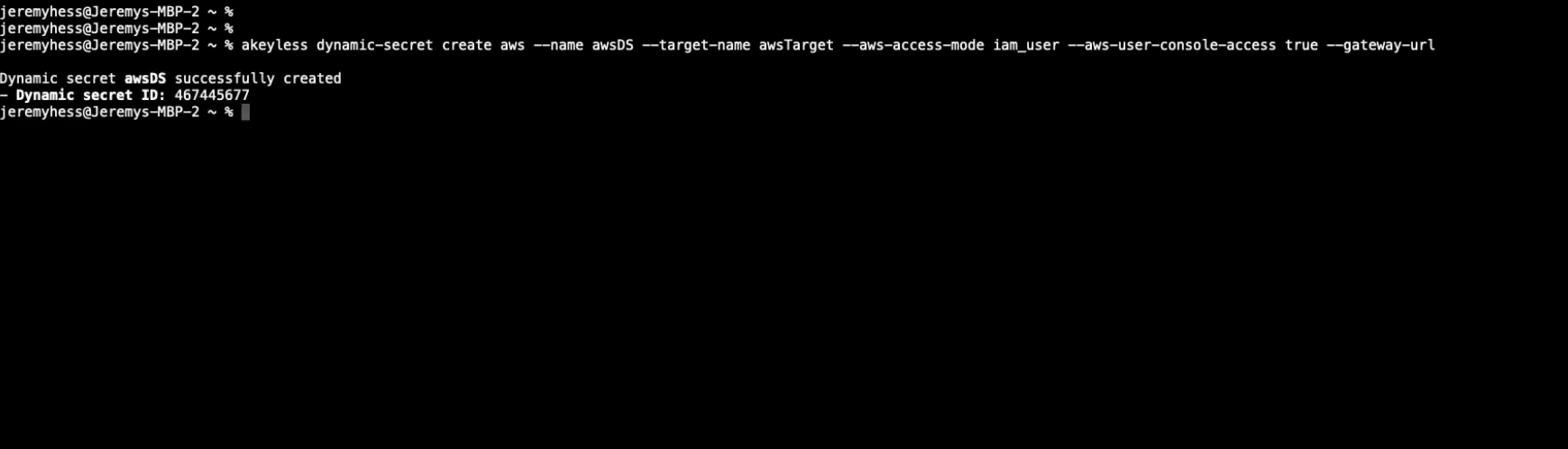
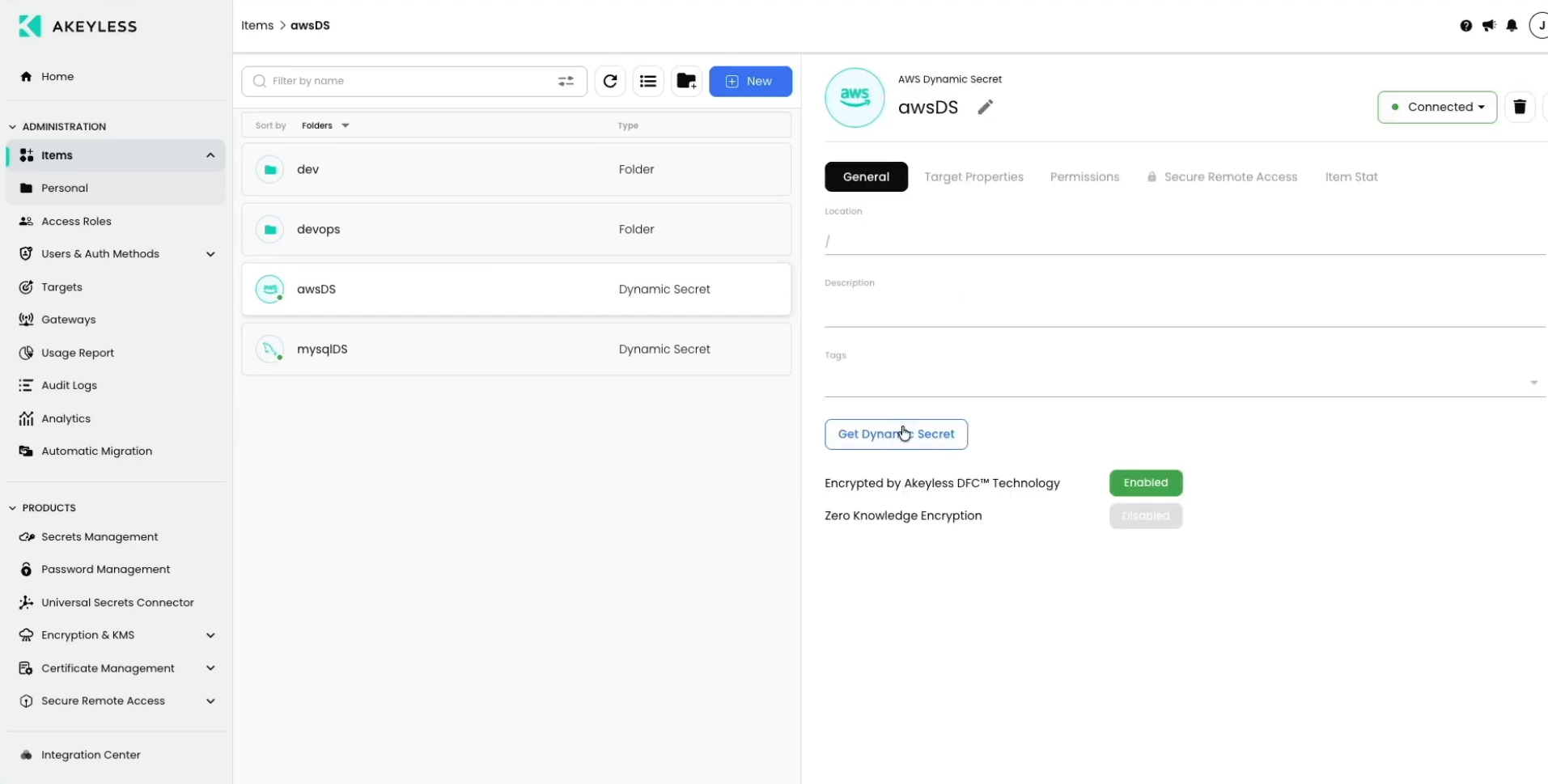
And you will be able to see the Dynamic Secret created in the Console as well:
Get a New Dynamic Secret via the CLI
Use the following command to fetch a new Dynamic Secret:
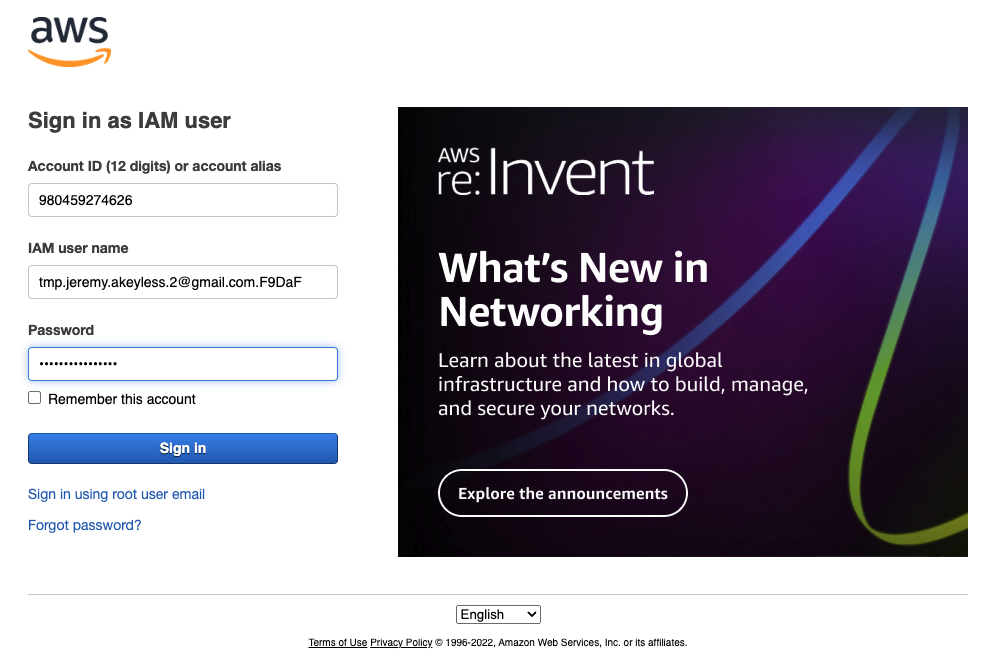
akeyless get-dynamic-secret-value --name <path_to_dynamic_secret>You will then see the following information that can be used to login to your AWS Console:
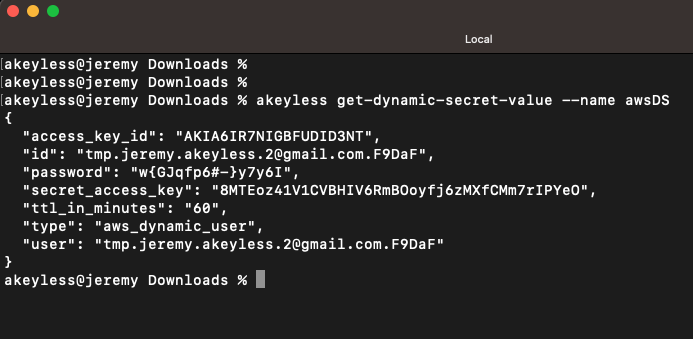
These details 'id' and 'password' can now be used for 60 minutes to login to your AWS account:
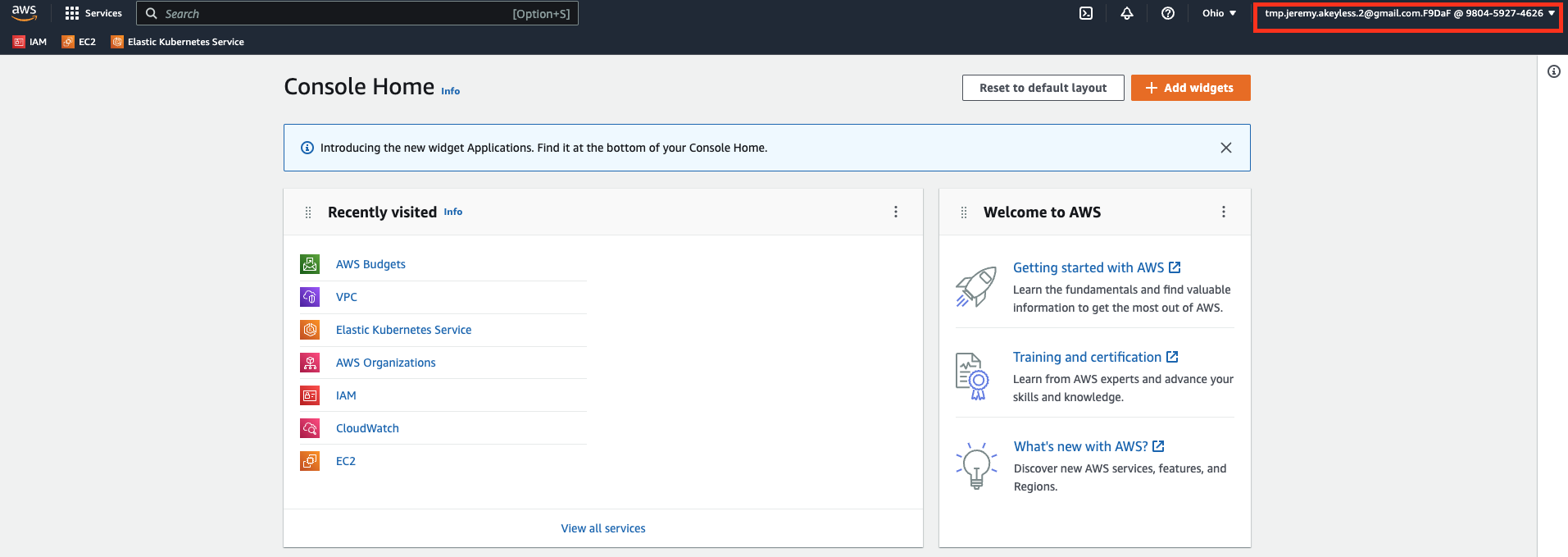
Notice that you have the temporary 'IAM user name' on the top right corner when logged in:
Updated 12 days ago
